Table of Contents
Goal
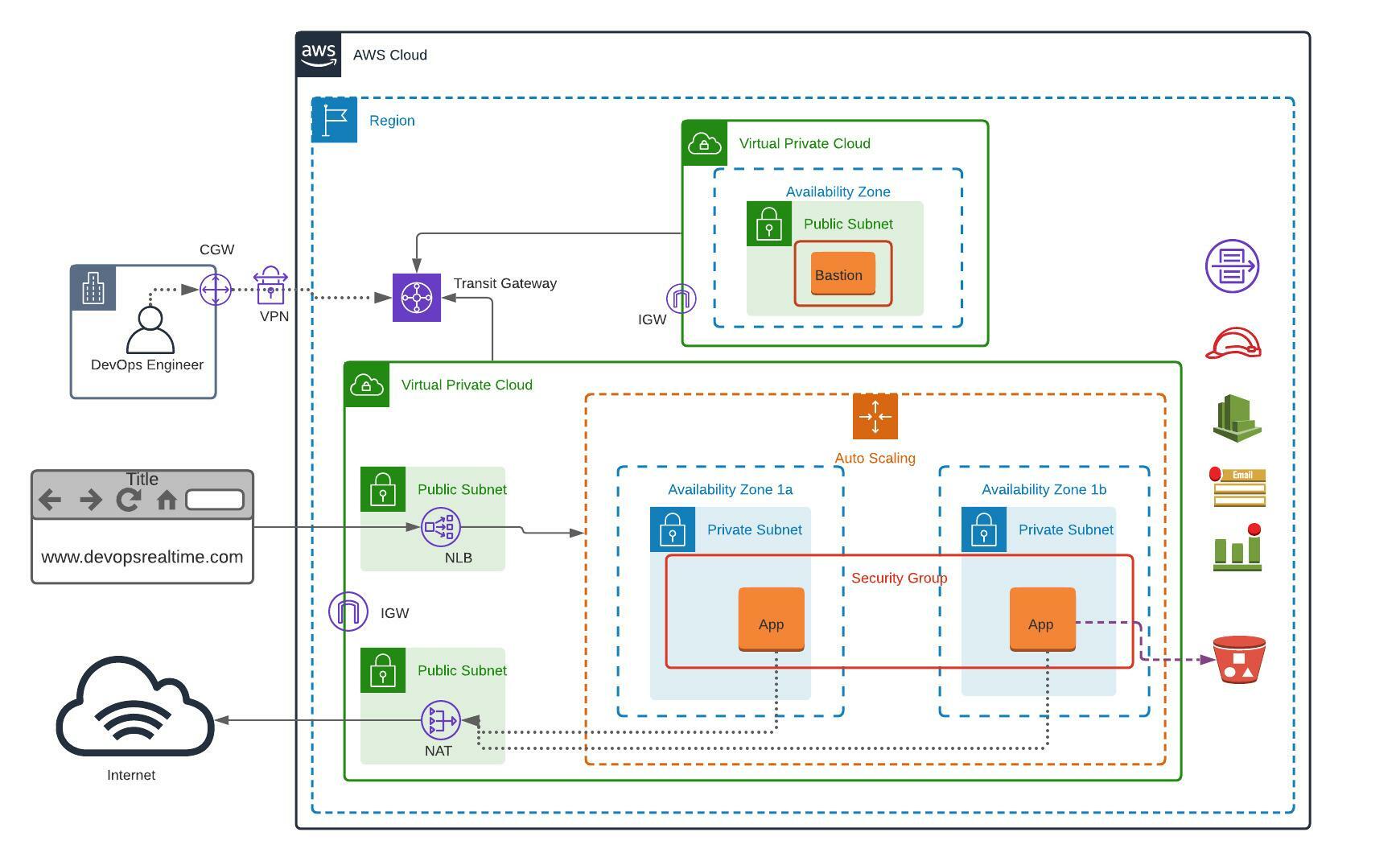
Deploy a Modular and Scalable Virtual Network Architecture with Amazon VPC.
Pre-Requisites
- You must be having an AWS account to create infrastructure resources on AWS cloud.
- Source Code
Pre-Deployment
Customize the application dependencies mentioned below on AWS EC2 instance and create the Golden AMI.
- AWS CLI
- Install Apache Web Server
- Install Git
- Cloudwatch Agent
- Push custom memory metrics to Cloudwatch.
- AWS SSM Agent
VPC Deployment
- Build VPC network ( 192.168.0.0/16 ) for Bastion Host deployment as per the architecture shown above.
- Build VPC network ( 172.32.0.0/16 ) for deploying Highly Available and Auto Scalable application servers as per the architecture shown above.
- Create NAT Gateway in Public Subnet and update Private Subnet associated Route Table accordingly to route the default traffic to NAT for outbound internet connection.
- Create Transit Gateway and associate both VPCs to the Transit Gateway for private communication.
- Create Internet Gateway for each VPC and Public Subnet associated Route Table accordingly to route the default traffic to IGW for inbound/outbound internet connection.
- Create Cloudwatch Log Group with two Log Streams to store the VPC Flow Logs of both VPCs.
- Enable Flow Logs for both VPCs and push the Flow Logs to Cloudwatch Log Groups and store the logs in the respective Log Stream for each VPC.
- Create Security Group for bastion host allowing port 22 from public.
- Deploy Bastion Host EC2 instance in the Public Subnet with EIP associated.
- Create S3 Bucket to store application specific configuration.
- Create Launch Configuration with below configuration.
- Golden AMI
- Instance Type – t2.micro
- Userdata to pull the code from Bitbucket Repository to document root folder of webserver and start the httpd service.
- IAM Role granting access to Session Manager and to S3 bucket created in the previous step to pull the configuration. (Do not grant S3 Full Access)
- Security Group allowing port 22 from Bastion Host and Port 80 from Public.
- Key Pair
- Create Auto Scaling Group with Min: 2 Max: 4 with two Private Subnets associated to 1a and 1b zones.
- Create Target Group and associate it with ASG.
- Create Network Load balancer in Public Subnet and add Target Group as target.
- Update route53 hosted zone with CNAME record routing the traffic to NLB.
Validation
- As DevOps Engineer login to Private Instances via Bastion Host.
- Login to AWS Session Manager and access the EC2 shell from console.
- Browse web application from public internet browser using domain name and verify that page loaded.
Solution:
Follow the LINK to get the complete solution of this project.
Follow the LINK to get the Project documentation
Follow the LINK to get the configuration files used in this project
© Edwiki Trainings – Click HERE If you are interested to learn more on Cloud & DevOps stack.







13 comments
Customer gateway (CGW) and VPN are shown in the architecture are for connecting to the AWS VPC using private tunnel. You can ignore this from the deployment as CGW is require to setup the VPN at On-Prem datacenter side.
I’ve been able to successfully complete all parts of the assignment. This was an all encompassing lab (thanks PR!) that required me to do some research on creating the approriate routes for the transit gateway. I will try to put my console snapshots together for anyone interested
I am not able to add/select the Nat GW while adding route for pvt subnet route table in vpc -2 (172.32.1.0/24) private subnet. since we have to create nat gw in public Subnet ( 192.168.1.0/24 ),.Could you please suggest?
NAT and Route Table must be in the same VPC. You might have created the both resources in different VPC. Check once again and make sure the resources are in same VPC.
In this scenario the NatGW and pvt subnet route table are belongs to different vpc , Then how to implement the routing of default traffic to NATGW for outbound internet in vpc-2.
You need to put a route in the private route table with the nat gateway as the target. If you dont see the nat gw, as pr mentioned you most likely created the nat gw in a different vpc
check my github repo
https://github.com/yemisi/Valaxytraining
You will find an image of routing rules for the private route table with nat gw as target. THERE ARE SCREENSHOTS OF all configurations IN A PDF AND DOC FILE THAT MIGHT HELP WITH COMPARING YOUR WORK.
I have been able to complete all steps of the assignment. Thanks for including new CONCEPTS (TGW, NAT Gateway and ASG, VPC Flow logs) in assignment. it improves confidence and exploring new things and IMPLEMENTING.
I have completed the task successfully.
Userdata to pull the code from Bitbucket Repository to document root folder of webserver and start the httpd service.
— In above point, we can add the git commands in the launch configuration right.
ComplEted above assignment.
Completed
it was a task worth taking on. the first time i didn’t quite get all the resources to work but i was successful the second time. i’m happy
Please share videos sir